Microsoft 365: Why the “Out of the Box” Solution Is Not Fully Secure
Microsoft 365 is one of the most popular software packages for the small business right up to the large-scale enterprise. And it’s no wonder – the toolbelt of easy-to-use applications addresses nearly every business administration problem while also enabling first-rate integration and collaboration.
Because of its popularity, 365 needs robust security options that take advantage of the latest technology to protect companies from cyber attackers. However, do the “out of the box” security options for 365 cut it, or are there elements of the package that aren’t entirely secure?
Continue reading our guide to 365s security options and how it should be more secure.
Why is Office 365 not a fully secure option?
Microsoft’s Office 365 ‘out of the box’ isn’t fully secure for the average Australian organisation for a number of reasons which we will cover below. The first key point to raise is that it doesn’t quite meet the recommended standards of the ACSC Essential Eight without some important reconfiguration of the default settings.
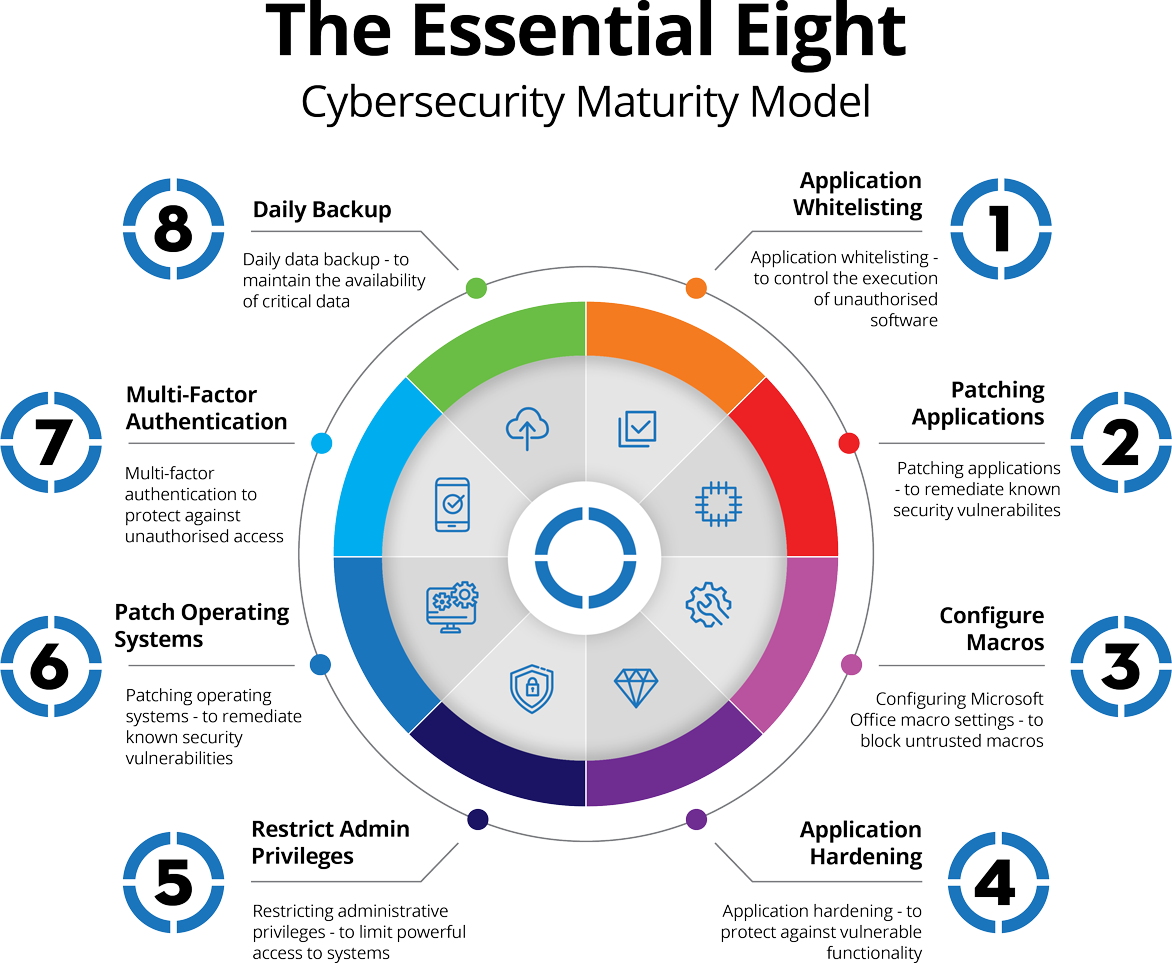
The Essential Eight
The Essential Eight consists of eight central strategies designed by the ACSC (Australian Cyber Security Centre) to help Australian organisations mitigate or prevent cybersecurity incidents. These strategies cover three key areas – prevention, limitation, and recovery – ranked by four maturity levels. The eight main areas of interest include: application control, patching applications, configuring Microsoft Office macro settings, user application hardening, restricting administrative privileges, patching operating systems, multi-factor authentication, and regular backups.
Based on the Essential Eight there are some important questions you should ask when it comes to your organisation’s IT environment and Office 365 configuration:
- Are all of Microsoft’s recommended block rules implemented?
- Are Microsoft Office macros disabled for users that do not have demonstrated business requirement?
- Is Microsoft Office macro antivirus scanning enabled?
- Have you ensured that Microsoft Office macro security settings cannot be changed by users?
- Are all Microsoft Office macro executions centrally logged and protected from unauthorised modification and deletion, monitored for signs of compromise, and actioned when cyber security events are detected?
- Are only privileged users, who are responsible for validating that Microsoft Office macros are free of malicious code, able to write and modify content within Trusted Locations?
- Have you ensured Microsoft Office macros digitally signed by an untrusted publisher, cannot be enabled via the Message Bar or Backstage View?
- Is Microsoft Office blocked from creating child processes, from injecting code into other processes and creating executable content?
If you answered “no” to any of the questions above, your Office 365 might have a few holes that malicious actors could poke their fingers through to gain access to your critical data.
Although Office 365 has a vast number of security options, essentially Microsoft’s approach has been to put the controls of protecting your data into your own hands. The issue with this is most people are not experienced security professionals, leaving many businesses vulnerable and open targets for the common cybercriminal. Some of the main reasons that Office 365 is not entirely secure include:
1. Important Security Features Are ‘turned-off’ by default
As a business owner who has implemented Microsoft for your organisation, it is well justified to think that such a notable and widely used product should by default have all the security features enabled from the start, however, this is not the case.
For instance, some of the following settings may need to be reconfigured to fully secure your 365 environment.
- Multi-Factor Authentication (MFA) for Administrators and Users
- Idle session signout
- Blocking legacy authentication
- Password expirations and banned password lists
- Permissions for external sharing
- Account lockout threshold
- Mobile application management
- Client forwarding rules
- Consent for un-managed applications
Additionally, there are other issues of secure backup strategies, retention policies and also end-user training and guidance on best security practices.
2. Smaller Businesses don’t have access to the advanced security services
Although smaller businesses can likely afford the basic package of Office 365 with the basic security services, some critical elements are only available with the advanced tier.
For example, the basic tier doesn’t include protection for a company’s devices, such as mobile devices, laptops, tablets and more. If these devices don’t have protection, a cyber attacker can inject malware and corrupt critical business data.
Microsoft 365 security features for the basic tier don’t include protection against malicious attachments. These can consist of email attachments, URLs and essential files. If a company doesn’t have this Office 365 security feature, it can suffer from data corruption, data theft and more.

3. It is a perfect target for cyber attackers
A sign that Office 365 is not entirely secure is that it has been a significant target for cyber-attacks. Criminals have been targeting its users for a few simple reasons, most notably that a large amount of data is not safely stored in the more secure premium tier.
Office 365 has many apps and services for creating files and documents containing sensitive information; the data on these platforms is very valuable to cyber attackers. Excel is especially at risk because it can contain extensive databases with information that could damage a company if leaked or corrupted.
Additionally, the features that aren’t on the basic 365 tier are common knowledge, so cyber attackers know precisely how to target a small business – often by using basic publicly available hacking software and simple social engineering tactics.
The main features not on the premium tier include device security and dangerous attachment protection. Cybercriminals will focus on these to exploit the protection that 365 won’t give small businesses.

4. It lacks an advanced monitoring tool to detect potential cyber attacks
Although Microsoft 365 does its best to protect against cyber-attacks when they happen, the tools it has to watch for attacks from cybercriminals aren’t as extensive as some of its competitors.
Monitoring is a powerful tool that can help a security system find malware, suspicious attachments and other attacks and report them to a company. The best monitoring tools will include 24/7 monitoring services (and global navigation for the most expansive search), enabling a constant and consistent scanning for potential threats.
Unfortunately, the monitoring for Office 365 is quite basic; the tools on the system only watch for incoming cyber-attacks; they lack the capabilities of preemptively putting in strong roadblocks for cybercriminals.
A final summary on why Microsoft 365 is not fully secure ‘out of the box’
Microsoft 365 has many excellent security offerings for small and large companies, however, as we discussed it isn’t fully secure for the average Australian small business. This presents a perfect scenario for cybercriminals to take advantage of unsuspecting victims.
The ACSC have developed a comprehensive standard for cyber resilience known as the Essential Eight. This standard outlines 4 maturity levels for businesses to operate in-line with and extensively details what needs to be in place regarding Microsoft 365. In contrast with this, Microsoft/Office 365 ‘out of the box’ solution doesn’t quite cut it from a cybersecurity perspective and requires some key reconfigurations of security features that are not set by default.
If you haven’t already done so, it is highly recommended that you perform a security risk assessment for your business and ideally scale it against the Essential Eight. This way any vulnerabilities can be brought into the light, and you can plug any holes to reinforce your cyber resilience.
If you need assistance with a risk assessment for your business, IT or need help with ‘hardening’ your Microsoft/Office 365 feel free to get in touch with our cyber specialists.