How Cybersecurity and Compliance Work Together
Cybersecurity and compliance often go hand-in-hand; in many ways, they’re two sides of the same coin. However, it’s a mistake to treat the two as interchangeable since they have important differences. Your organisation shouldn’t be focusing on one or the other – both of them need to operate in tandem as part of the same constant process.
So how do cybersecurity and compliance work together? To understand their relationship, it’s important to first mark out the differences in how the two operate.
What is Cybersecurity?
Cybersecurity is the process of defending an organisation’s networks, IT systems, software, websites and valuable data from attacks by cybercriminals. As implied by its name, this usually centres around the technological aspects of an organisation. However, cybersecurity also works to ensure that the people and processes in an organisation are also fully prepared to prevent data breaches.
An effective cybersecurity strategy is comprehensive and wide-reaching, assessing the entire organisation to identify risks and vulnerabilities and determining how best to either fix or mitigate them. This includes physical and administrative processes as well as technical considerations.
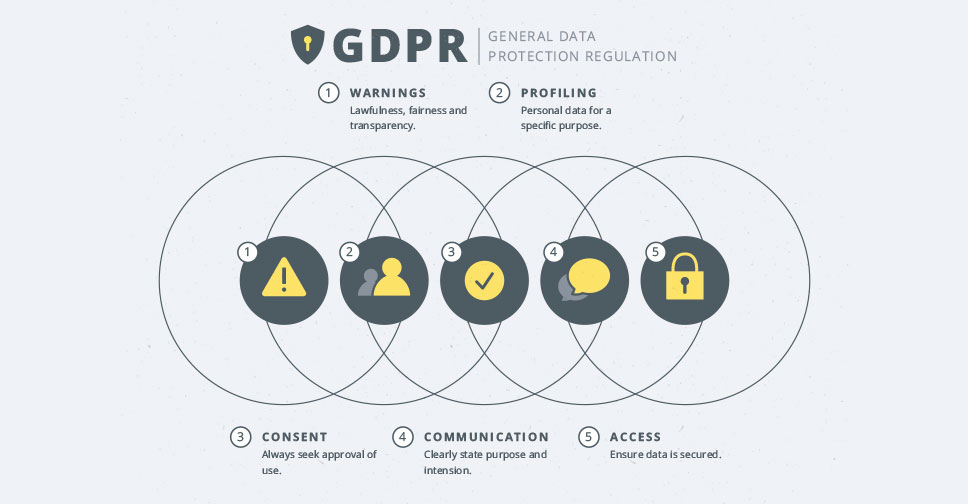
What is Compliance?
While cybersecurity looks inwards to assess an organisation’s measures to protect against cyberattacks, compliance instead looks outwards. Compliance is the process of understanding and meeting the requirements of legislation, industrial standards and third parties (such as regulatory bodies, clients or suppliers) in relation to protecting sensitive data types.
Compliance can be a complex task to unravel, since an organisation may be bound by multiple compliance frameworks – it may face legal regulations such as Australian Privacy Principles (APPs), or industry-specific requirements such as those laid out by the Payment Card Industry Data Security Standard (PCI DSS), and additional requirements set out by partner organisations or clients.
As such, compliance teams work to unravel the various compliance frameworks that apply to the organisation and create clear procedures, guidelines and documentation to ensure these frameworks are fulfilled and that evidence can be provided to auditors to prove this is the case.
So what’s the difference between Cybersecurity and Compliance?
One of the major differences between cybersecurity and compliance is what the two aim to protect an organisation from. Cybersecurity is focused on the risks posed to the organisation from cyber-attacks and data breaches.
Compliance, meanwhile, also involves measures to protect data, but its main aim is to protect the organisation from the consequences of failing to meet compliance frameworks set out by third parties. For example, failure to adhere to a regulatory body’s standards may result in costly fines to the organisation.
What this boils down to is the fact that even the best cybersecurity strategy may not satisfy compliance frameworks, and conversely, strictly adhering to compliance frameworks doesn’t necessarily mean your organisation is invulnerable to cyber-attacks.
It’s therefore important to take a blended approach to cybersecurity and compliance. The two disciplines work best when they inform and complement each other in a cooperative process, rather than treating them as two distinct processes.
How Cybersecurity and Compliance work best together to protect your organisation
As mentioned above, a key part of a compliance team’s work is to prove to regulators and other third parties that compliance frameworks are being fulfilled. This requires evidence in the form of comprehensive documentation.
This means that communication between compliance and cybersecurity teams is vital. From the outset, compliance teams need to make sure the requirements of relevant compliance frameworks are made clear to cybersecurity teams, and cybersecurity teams should be clear in detailing how they fulfil these obligations.
In this way, compliance teams can guide cybersecurity teams in creating cybersecurity measures that are both robust and in line with regulations, with clear details such as the specific firewall types, protocols and security standards that are necessary and which data types are most important.
The cybersecurity team can then provide clear documentation of how these requirements have been met and avoid having to rebuild or replace non-compliant security measures further down the line. The comprehensive documentation required by compliance teams can also benefit cybersecurity, as clear development histories can make it easier to identify when and where problems arise and leave clear frameworks for implementing similar solutions in future.
Cybersecurity and compliance teams can also work together in automating processes to the benefit of both. For example, automation can streamline document generation, collection and storage, giving compliance teams easy access to evidence they can provide to auditors, saving time and effort in reporting and reducing the possibility of human error.
Outsourcing Compliance and Cybersecurity
One solution to ensuring a complementary approach taking in both compliance and cybersecurity is to outsource these processes to a third-party cybersecurity and compliance expert.
Both cybersecurity and compliance are technical subjects and can be extremely complex – cybersecurity due to the ever-evolving nature of cyber attacks, and compliance due to the number of complicated and conflicting frameworks your organisation may have to follow.
Outsourcing to a professional cybersecurity and compliance service ensures that you have access to the necessary knowledge and expertise to satisfy the needs of both, whilst also allowing a unified approach by having both cybersecurity and compliance handled by a single entity. Another benefit is that outsourcing saves your organisation time and effort which could be more productively spent fulfilling its ordinary operations.
Whether you choose to outsource or handle compliance and cybersecurity in-house, taking an approach that allows the two processes to inform and complement one another is the key. At the end of the day, keeping your organisation safe from data breaches and cyberattacks whilst ensuring all the requirements of third parties are satisfied, is crucial as we speed further into the future of the online marketplace.